Telegram Marketing: How to Avoid Bans with the Right Gateway Setup
Scaling Telegram automation is often treated as a behavioral problem. Most operators focus on delays between actions, account warm-up, and message limits. Even when these elements are well optimized, issues such as random bans, session instability, and inconsistent performance still appear. At scale, this assumption breaks. The problem is not behavior. It is the network layer behind each connection.
If you’ve worked with Telegram automation, you’ve likely seen this pattern: everything is “optimized” – delays are human‑like, accounts are warmed up, and sending limits are respected. Yet, over time, some accounts get banned, others lose performance, and identical setups behave differently. At first, this feels like a behavioral issue. But as operations scale, a contradiction appears: accounts following the same logic produce completely different results. This is where most operators misdiagnose the problem. Telegram is not just evaluating what your accounts do – it’s evaluating who they appear to be on the network.
Why Telegram Automation Fails at Scale
Most automation strategies focus on behavior: slower actions, reduced activity spikes, and randomized patterns. These techniques work in early stages. At scale, a different layer becomes dominant: connection origin, network consistency, and IP history. This is why small setups often work, while larger ones suddenly become unstable. Scaling doesn’t just increase volume — it amplifies inconsistencies.
How Telegram Evaluates Accounts and Connections
Key Signals Behind Every Connection
Each connection carries multiple signals: IP type (mobile, residential, datacenter), ASN (network provider identity), historical activity of that IP, geographic behavior over time, and overlap with other accounts. These signals are not analyzed in isolation. They are combined into a broader model.
What Is Network Identity
All these elements form what can be described as a network identity — a persistent profile that answers a key question: does this account behave like a real, consistent user over time? Two accounts can perform identical actions, but if their network identity differs, outcomes will also differ.
Same Setup, Different Results — What Changes?
You may run the same script, timing, and workflow, and still see one account stable for weeks while another gets banned within hours. The difference is rarely in the script.
Network Reputation Inheritance
Every IP has a history. In practice, this means an IP used for aggressive automation may already carry risk, or an IP previously flagged may be under stricter scrutiny. When your account connects through that IP, it inherits part of that reputation. This explains why fresh accounts can get banned quickly, even with clean behavior. You are not starting from zero — you are entering an existing context.
The Hidden Risk of Contaminated Gateway Environments
Shared IP Relays and Unknown History
Many gateway solutions rely on shared IP pools, rotating networks, or heavily reused infrastructure. In these environments, multiple users operate on the same IP, activity patterns overlap, and history is unpredictable.
Why Clean Behavior Is Not Enough
Even if your automation is well‑designed, the environment may not be. A common real‑world pattern looks like this: accounts perform normally at first, message delivery gradually drops, session stability declines, and bans occur without a clear trigger. This creates the illusion of randomness. In reality, the issue was already embedded in the network environment.
Why Telegram Bans Seem Random (But Are Not)
Accumulated Risk and Scoring Systems
Telegram likely evaluates accounts using a scoring model. Each inconsistency adds risk, each unusual pattern contributes to the score, and each session reinforces or weakens trust.
Threshold‑Based Detection
A typical pattern observed in operations: the account works normally for hours or days, performance starts degrading, restrictions appear gradually, and then a full ban occurs. The ban is not a single event — it is the result of accumulated signals crossing a threshold.
Geographic Consistency as a Trust Factor
Alignment Between Number, IP, and Session
Telegram evaluates whether your account’s behavior is geographically coherent. For example, a Brazilian number consistently connecting from Brazil looks natural, while the same number switching between multiple countries quickly does not.
Common Geographic Mistakes
Common mistakes include using accounts registered in one country with IPs from another, switching regions frequently, rotating IPs aggressively across countries, and constant changes in network provider (ASN). These patterns are rarely seen in real users and significantly increase long‑term risk.
The Core Principle: Network Identity Persistence
Stable operations follow a simple principle: maintain a consistent network identity over time. In practice, this means stable region, predictable IP behavior, and gradual changes instead of abrupt ones. Accounts that maintain consistency tend to build trust, experience fewer bans, and behave more predictably. Trust in Telegram is not granted — it is accumulated through consistency.
Why Most Gateway Strategies Fail
More IPs Does Not Mean More Stability
A common reaction to bans is adding more gateways, increasing rotation, or switching providers. But this often makes things worse. Without control, more IPs mean more unknown history, more inconsistencies, and more noise.
Lack of Control Over IP Usage
If you don’t control who used the IP before, how frequently it’s reused, or how many accounts share it, you are introducing invisible risk.
The Importance of Account Isolation
In shared environments, multiple accounts may perform similar actions within the same time window using the same IP. This creates detectable patterns such as synchronized activity, repeated behavior sequences, and correlated session data. These correlations significantly increase detection probability. At scale, isolation becomes essential.
What Actually Works for Telegram Automation
Dedicated IP per Account
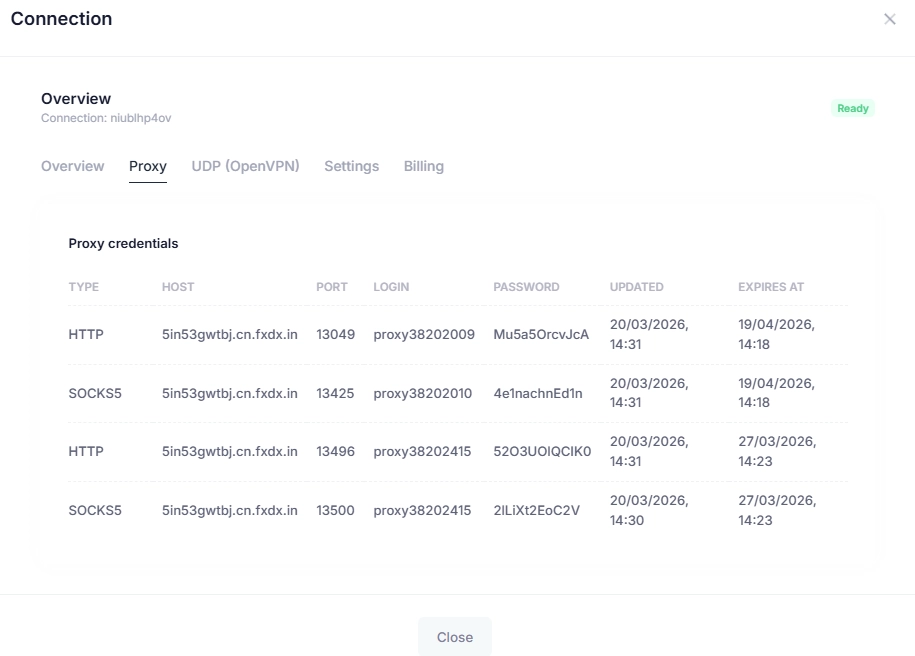
Each account should operate on a dedicated IP to prevent overlap and eliminate shared risk.
Real Mobile Carrier IPs
Mobile IPs tend to reflect real user environments, introduce natural variability, and generate stronger trust signals. However, quality and history matter more than category alone.
Controlled IP Rotation
A common mistake is rotating IPs too frequently in an attempt to stay safe. In reality, excessive rotation creates stronger automation signals than stability. Accounts that maintain the same IP for longer periods with occasional, controlled changes tend to perform better.
Geographic Alignment
Matching IP location with account origin reinforces consistency across all signals. Misalignment introduces long‑term instability.
From Tools to Infrastructure
At small scale, automation is about tools. At large scale, it becomes about infrastructure. The shift is from execution to control, from scripts to consistency, and from actions to identity. Tools execute actions. Infrastructure determines whether they survive.
NafeProxys: Infrastructure Built for Network Identity Control
Most gateway providers focus on access. NafeProxys focuses on control and predictability. It is designed to eliminate the main risks that cause instability in Telegram automation.
Eliminating IP Contamination
Dedicated connections ensure no shared usage, reducing inherited risk.
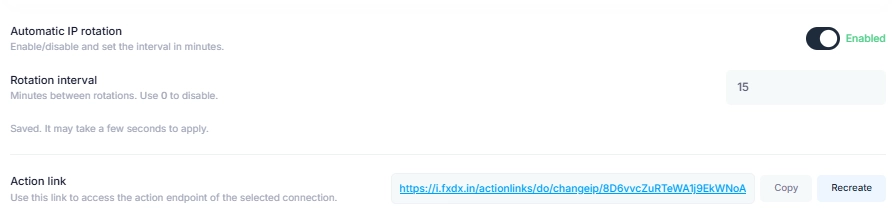
Controlled Rotation (Rotation URL)
IP changes can be triggered programmatically, allowing predictable and scalable automation.
Clean Sessions (Skip Used IP)
Previously used IPs are not reused, reducing exposure to historical risk.
Custom DNS for Network Consistency
Precise traffic routing ensures alignment across all connection layers.
Centralized Dashboard and Visibility
You can monitor sessions, manage connections, and maintain full operational control.
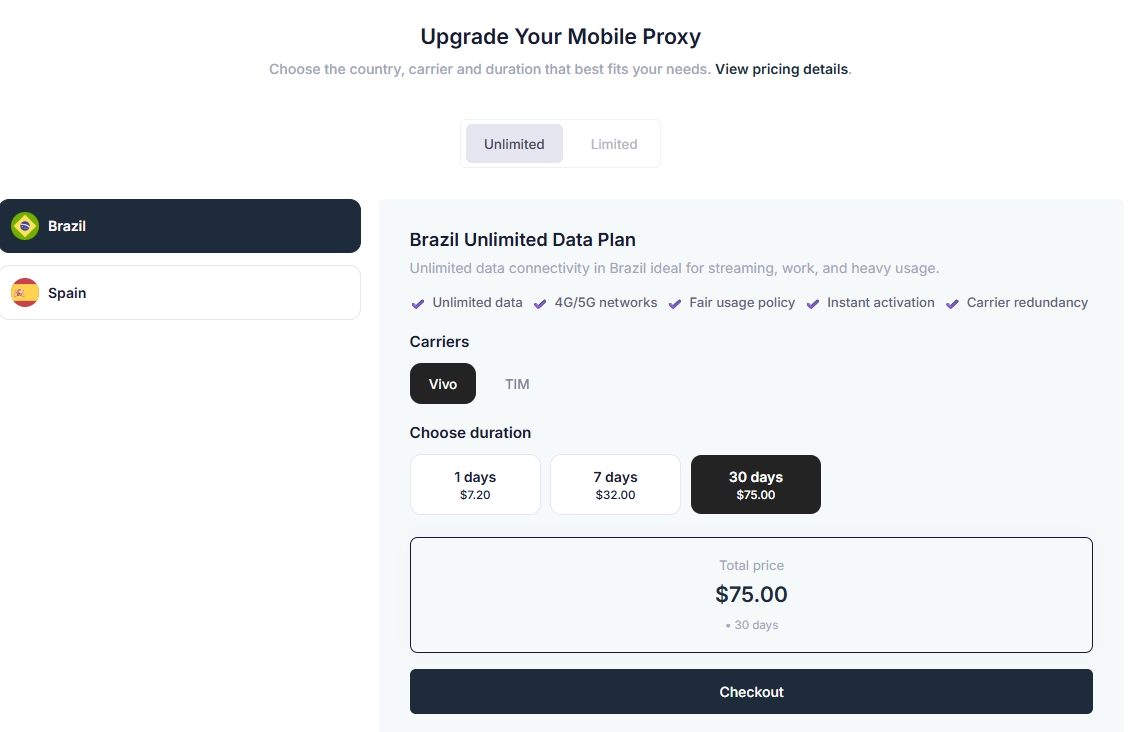
Real Mobile Carrier Infrastructure
NafeProxys uses real telecom IPs in Brazil and Spain, creating more natural connection patterns.
Dedicated Connections and Isolation
No shared IP pools and no cross‑account contamination, ensuring consistent performance.
🔐 Secure Encrypted Tunnel
Built on encrypted tunnel infrastructure, ensuring:
encrypted and secure connections
stable sessions for ad accounts
reduced risk of unexpected disruptions
A secure connection is the foundation of a trusted network identity.
Conclusion: Stability Comes from Network Control
If your Telegram automation is unstable, the issue is not just behavior. It is your network. Behavioral optimization has limits. Without control over IP quality, network identity, and connection consistency, results remain unpredictable.
When infrastructure is properly designed with clean IPs, dedicated connections, and geographic alignment, bans become less frequent, performance becomes stable, and scaling becomes possible. Telegram automation is not about doing more actions. It is about maintaining a consistent identity over time. And at scale, that identity is defined by your network.

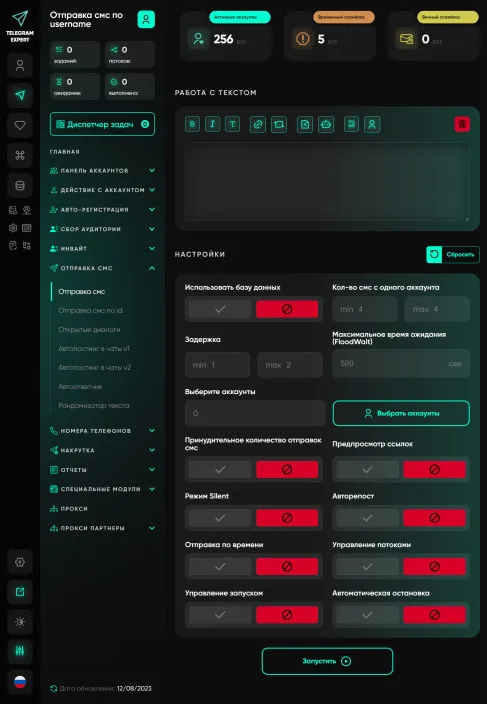
Download Telegram Expert - software for Telegram promotion
Telegram Expert is professional software for fast channel growth and sales in Telegram. Launch mass mailings and invites, warm up accounts without bans, consolidate dialogs in one place, and scale your team. All in one window - fast, safe, and tailored to your tasks.
What it can do:
- TDATA Converter - массово переводит session+json в TDATA.
- Booster - account warm-up via smart dialogs to increase trust.
- Registrar - account creation via any SMS services with the sms-activate standard.
- Duplicator - a second session for existing accounts for transfer and protection.
- Forwarder - routes incoming replies to a working group and sends replies to clients.
- Interceptor - catches messages by keywords from chats/channels and forwards them to you.
- Invite via admin - invitations even to restricted groups.
- Channel and chat cloner - full copies, including protected content.
- Reporter - mass complaints about messages/users/channels.
No one has left a comment yet
Sending messages
We understand that messaging is a critical aspect of your job, whether you're a Telegram marketer, communicating with clients, or managing groups. Our program gives you the ability to send messages to groups and users using a powerful tabular database, allowing you to work efficiently and reach your audience with maximum accuracy. Telegram Expert provides you with a wide range of settings for sending messages. You can select your audience based on various parameters such as gender, photos, premi...
More Than Telegram: How to Safely Redirect Traffic to the Web and Interact with Strict Anti-Fraud Systems
Hello! You already know perfectly well that creating a powerful bot network and successful mailings within a messenger requires quality software, good network gateways, and competent session management. Within the Telegram ecosystem, our program handles tasks 100% effectively. But let's look wider. The ultimate goal of automation and traffic generation is almost always conversion on an external resource. Whether it's registration on cryptocurrency exchanges, farming accounts on Coinlist, uplo...
The 2026 Guide to Unlimited Residential Gateways: Scaling Data Collection Without Hitting a Wall
Data caps are the ultimate progress killer for web scraping and automation. If you manage large-scale market research or run multiple social profiles, the traditional pay-per-GB model creates unpredictable costs and sudden service interruptions. The industry has shifted dramatically. In 2026, the demand for unlimited residential IP infrastructure has skyrocketed. Businesses want predictable overhead and the freedom to scale operations without bandwidth anxiety. This guide breaks dow...
Telegram in Marketing: How to Scale Without Bans with MostLogin and Telegram Expert
Telegram is no longer just a messenger. Today, it is a powerful marketing ecosystem that companies use to attract and retain customers. But as the platform grows in popularity, so do the risks: account bans, action limits, and difficulties with scaling. How can you work in Telegram professionally without losing accounts? The answer lies in combining specialized automation software with an anti-detect browser. Let’s take a closer look at how MostLogin and Telegram Expert help build a stable promo...